Edge Point Protection
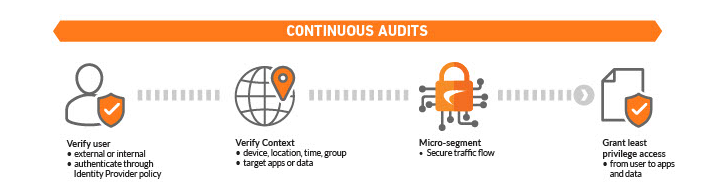
With the SonicWall Cloud Edge Secure Access, the perimeter is software-defined, meaning each micro-perimeter segment encapsulates a particular type of traffic flow, defined by access policies. The segment starts with the user and extends to specific networks or services or assets anywhere in the cloud — a much more versatile approach.
Cloud Edge Secure Access for Windows and mac OS proactively monitors the environment and automatically activates a secure access connection in public hotspots. This extra layer of protection stops Wi- Fi intercepts, which are increasingly common and can result in data thefts and compliance violation.
Kill switch – When a secure access connection is interrupted, the device’s internet connection is instantly halted — disrupting potential cyber breaches and preventing any data from leaving the device.
The core feature of any Zero-Trust environment is the creation of micro-perimeters around critical segments, also known as micro-segmentation. With the new NTC, the perimeter is software-defined and the built-in stateful firewall-as-a-service forms protective boundaries that control inbound and outbound network traffic.
NTC also acts as the Least-Privilege access manager, which allows an IT admin to deny or allow traffic from a specific user, device or location, and to a specific region, network, associated services and applications. As a result, every user can access only what’s necessary and nothing more — enabling complete “Zero-Trust Network Access Security.”
By limiting the exposure to other sensitive areas of the network, organizations can prevent threats from moving laterally, thereby securing their resources without sacrificing their operational flexibility.
Works Cited:
SonicWall. (2021). Cloud Edge Secure Access. Milpitas; SonicWall. https://www.sonicwall.com/medialibrary/en/datasheet/sonicwall-cloud-edge-secure-access.pdf
Cloud Edge Secure Access - A Cloud-Native Network-as-a-Service with Integrated Zero-Trust Security. (2020). Sonicwall.com. Retrieved June 12, 2023, from https://www.sonicwall.com/resources/videos/cloud-edge-secure-access-video/.



